Terrorism using biological and nuclear weapons : a critical analysis of risks after 11 September 2001
Kelle, Alexander ; Schaper, AnnetteDownload:
pdf-Format: Dokument 1.pdf (178 KB)
| URL | http://edoc.vifapol.de/opus/volltexte/2008/267/ |
|---|---|
| Dokumentart: | Bericht / Forschungsbericht / Abhandlung |
| Institut: | HSFK-Hessische Stiftung Friedens- und Konfliktforschung |
| Schriftenreihe: | PRIF reports |
| Bandnummer: | 64 |
| Sprache: | Englisch |
| Erstellungsjahr: | 2003 |
| Publikationsdatum: | 25.01.2008 |
| SWD-Schlagwörter: | Terrorismus , Biologische Waffe , Kernwaffe |
| DDC-Sachgruppe: | Politik |
| BK - Basisklassifikation: | 89.58 (Politische Gewalt) |
| Sondersammelgebiete: | 3.6 Politik und Friedensforschung |
Kurzfassung auf Englisch:
Ever since the Aum sect carried out a nerve gas attack in the Tokyo underground in March 1995, the likelihood of terrorist attacks with biological weapons (BW’s) has been a topic of public debate. In the weeks following the September 11th attacks in New York and Washington, D.C. in 2001, the occurrence of a number of cases of anthrax seemed to strongly support those who regarded the issue of whether terrorists would use biological weapons as already settled, leaving open only the questions of when and how such attacks were going to happen. In fact, this use of anthrax leads to the question of whether a paradigm change has occurred in the strategies and methods of terrorists, with biological weapons becoming a standard tool in the terrorist’s repertoire. Reviewed critically, the attack by the Aum Shinrikyo in Tokyo reveals two facts: on the one hand, the Japanese sect failed utterly in their attempts to produce biological agents and to use them as a weapon; on the other hand, none of the obstacles that were considered to affect the motivation of groups like Aum to obtain BW’s had any effect. The old worldview that terrorists are unlikely to use biological weapons has been thrown into question. The nature and the course of the terrorist attacks in the US can still be interpreted in a number of ways, however, all interpretations agree on two factors that are of key importance. Firstly, not only are Osama bin Laden and his organisation prepared to allow the death of thousands, they even make such multiple deaths a central element in the planning of their attacks. In this way, the old ‘rule’ of terrorism research, which maintains that terrorists are interested in creating large numbers of spectators but not of victims of their attacks, is challenged. Secondly, the use of pathogens in biological weapons, in the way seen recently, adds a new string to the terrorist’s bow. However in this case, BW’s were not used for mass destruction, nor is there evidence linking the attacks of September 11th and the anthrax letters. Talk of a new paradigm would only be justified if one of these were the case. The claim of a new way of thinking is, at best, premature and, at worst, leads to inappropriate political reactions. The Biological Weapons Convention (BWC) could be one of the first and, at same time, most dramatic, victims of the current focusing of the international public debate over the risk of biological weapons. The most recent review of this, which took place in Geneva between November 19th and December 7th 2001, was blatantly sabotaged by the US. The inevitable collapse of the review process could only be prevented by an adjournment until November 2002. The Biological Weapons Convention is the most useful multilateral instrument currently available for the formation of a line of defence against the threat of bioterrorism, amongst others. Failure would, therefore, be disastrous. In the past, it has been thought impossible that terrorists could build nuclear weapons. This assessment must, however, be reviewed. The theoretical principles are widely accessible to the public, with such information even being available on the Internet. However, at an engineering level, many technical details remain secret. The specialist capability and the techniques necessary for the ignition of nuclear weapons can only be acquired through several years of experimentation, which could not be hidden from the public. Therefore, a terrorist organisation would need the cover and protection of a state like Afghanistan. Given such protection, it would then be possible, in principle, for a terrorist organisation to develop the ignition technology, even without nuclear material. II The most difficult hurdle for a terrorist organisation is the procurement of nuclear fuel – plutonium or highly enriched uranium (HEU). In countries that are subject to the control of the International Atomic Energy Agency (IAEA), an illegal attempt to siphon off some nuclear fuel is likely to be detected at an early stage. The same is not true of those states that possess nuclear weapons but are not internationally controlled, Particularly in Russia, the national instruments for protecting and recording nuclear material are unsatisfactory. A few thefts have occurred and it is possible that terrorists have already got hold of nuclear material. That a terrorist group has the capability to produce this material can be ruled out. However, there are a few countries that have been or currently are suspected of developing nuclear weapons. They could possibly have supported or could in future support a terrorist organisation. Here, we discuss Iraq, North Korea, South Africa and Iran. A whole section is dedicated to Pakistan. Pakistan has always stressed that it does not pass on its nuclear weapons. However, little is known about Pakistani national security measures. It is not known whether religious fanatics could have access to nuclear material and could pass it on to terrorists. Cooperation with Pakistan should be considered as a means to achieve the physical protection of nuclear material. For several years, there have been growing indications that bin Laden is attempting to get hold of weapons of mass destruction. He has explicitly declared his wish to procure nuclear weapons and has tried to buy HEU on the black market. It is said that he also attempted to procure complete small nuclear weapons, so called “rucksack bombs”, originating from former Soviet stocks. A few years ago, a warning was issued that the stock of these weapons may no longer be complete. Terrorists could transport nuclear weapons by sea or by land. Such transport would probably not be discovered. A variant of nuclear terrorism that is technically much less challenging would be the use of a radiological weapon. Such a weapon is detonated by a conventional explosion and distributes highly radioactive material. Whole regions can, thus, be made uninhabitable. Another widely discussed scenario involves a passenger plane, with full fuel tanks, being crashed into a nuclear power station. However, the terrorists would have to be capable of hitting the shield vertically, in a nosedive, and not just scrape against it from the side. This is far more difficult than directing a plane into a high building. Several strategies exist that could reduce the risks of nuclear terrorism. These encompass, first and foremost, international cooperation to improve the security of nuclear material in Russia. It will also be necessary to cooperate with the three de facto nuclear weapon states, India, Pakistan and Israel, to increase the security of their nuclear facilities and materials. Current risk scenarios have to be reviewed, as they do not take into account the possibility that terrorists could aim for mass murder and are prepared to commit suicide. It would be appropriate to cooperate with the IAEA, which is involved in a variety of activities that aim to reduce the risks. The disposal of plutonium from disarmed nuclear weapons should be pushed forward. A further problem is the lack of an overview of the nuclear weapons currently in existence. An arms control treaty that includes the registration and disarmament of tactical nuclear weapons could reduce the risk of theft.
Für Dokumente, die in elektronischer Form über Datenenetze angeboten werden, gilt uneingeschränkt das Urheberrechtsgesetz (UrhG). Insbesondere gilt:
Einzelne Vervielfältigungen, z.B. Kopien und Ausdrucke, dürfen nur zum privaten und sonstigen eigenen Gebrauch angefertigt werden (Paragraph 53 Urheberrecht). Die Herstellung und Verbreitung von weiteren Reproduktionen ist nur mit ausdrücklicher Genehmigung des Urhebers gestattet.
Der Benutzer ist für die Einhaltung der Rechtsvorschriften selbst verantwortlich und kann bei Mißbrauch haftbar gemacht werden.
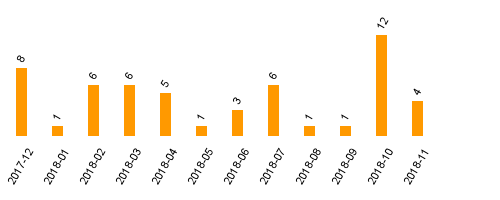
Zugriffsstatistik
(Anzahl Downloads)